Designed for the cloud, Spot Security is an agentless solution that gives you holistic visibility of your security posture in real time. Since not every issue can be addressed on day one, Spot Security provides an accurate, relevant list of misconfigurations, vulnerabilities and threats prioritized based on their urgency and criticality to your business, together with guided and automated remediation so you can fix them first.
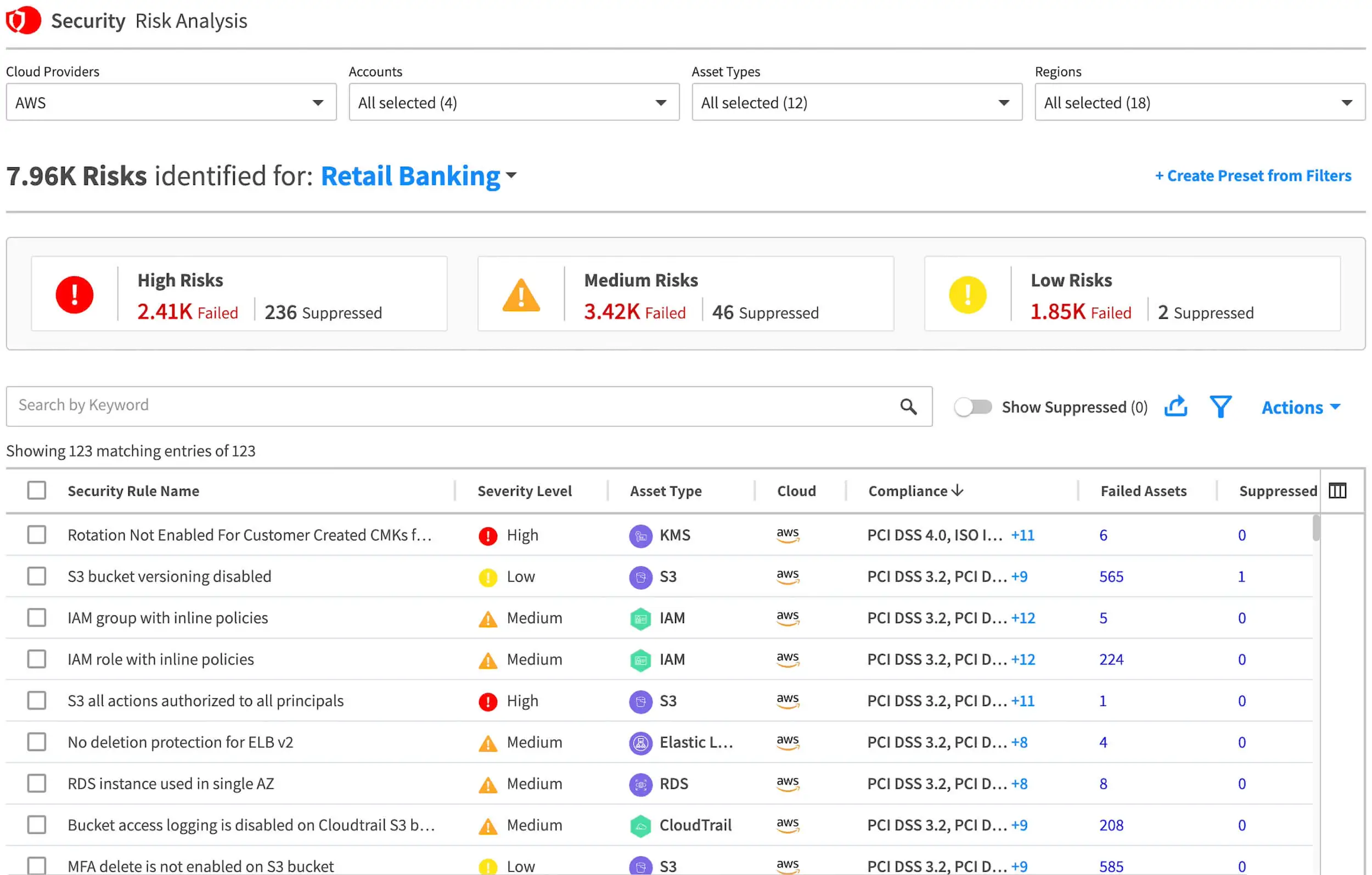
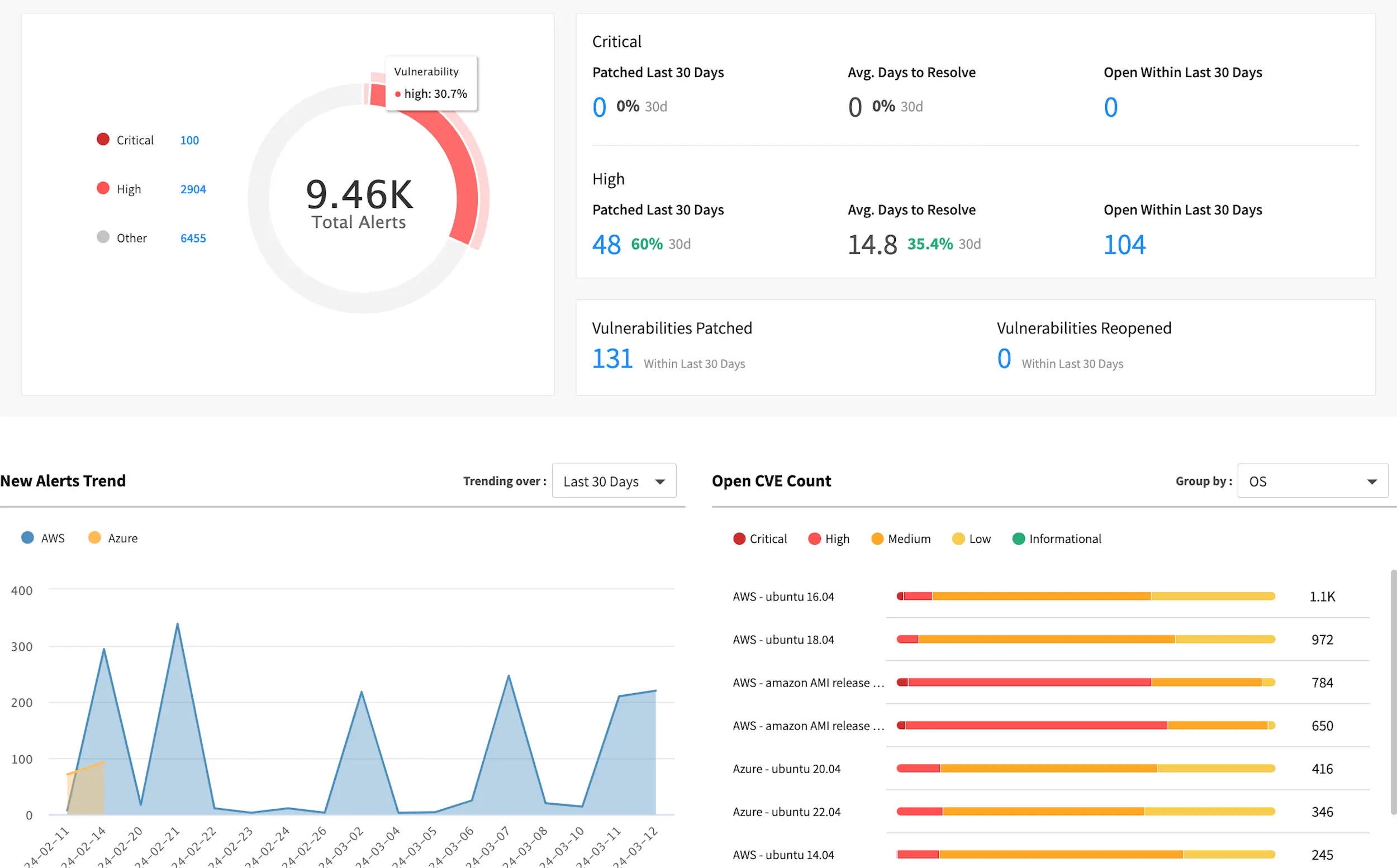
Fix the highest priority risks to your business in the least amount of time
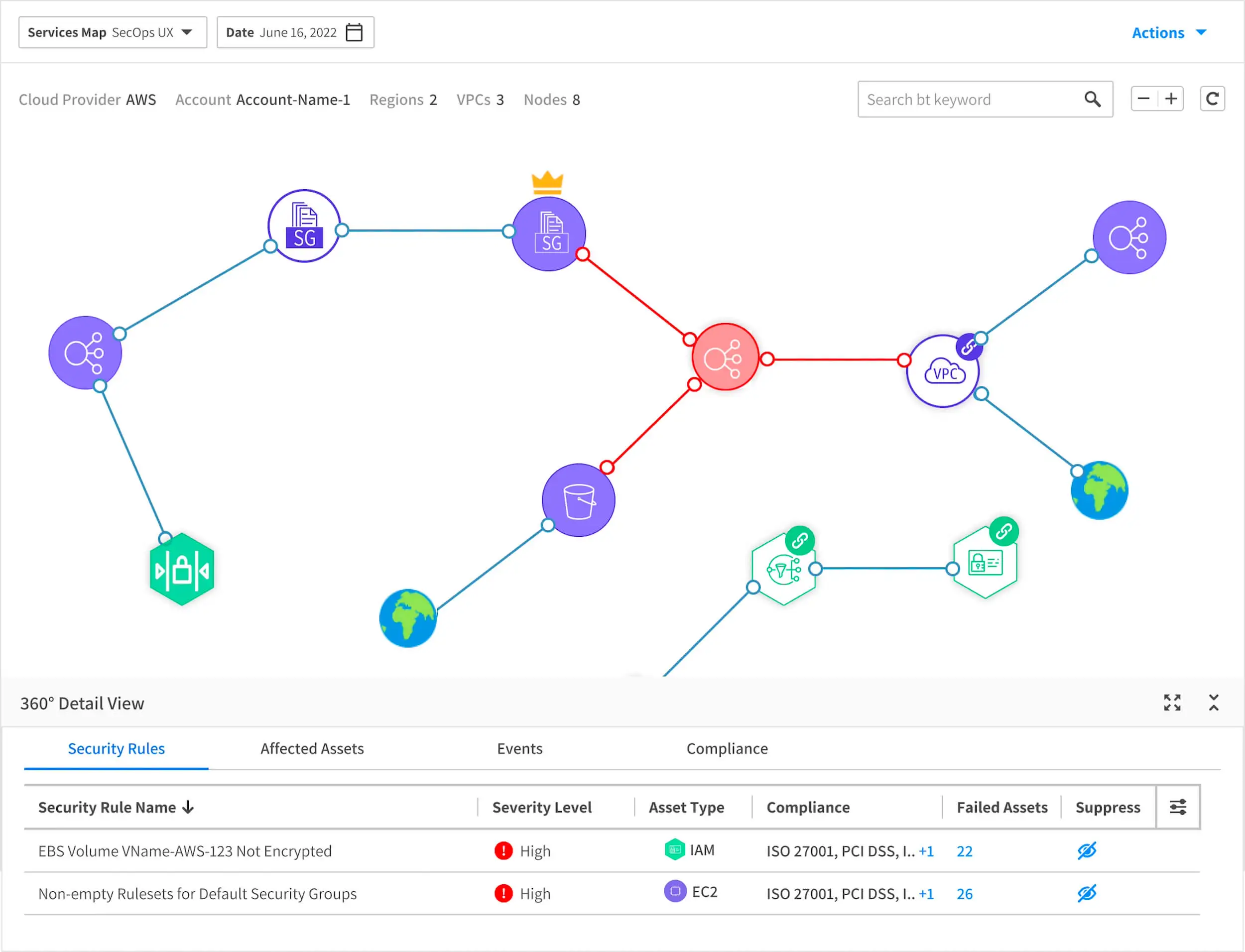
Gain a single view of your security
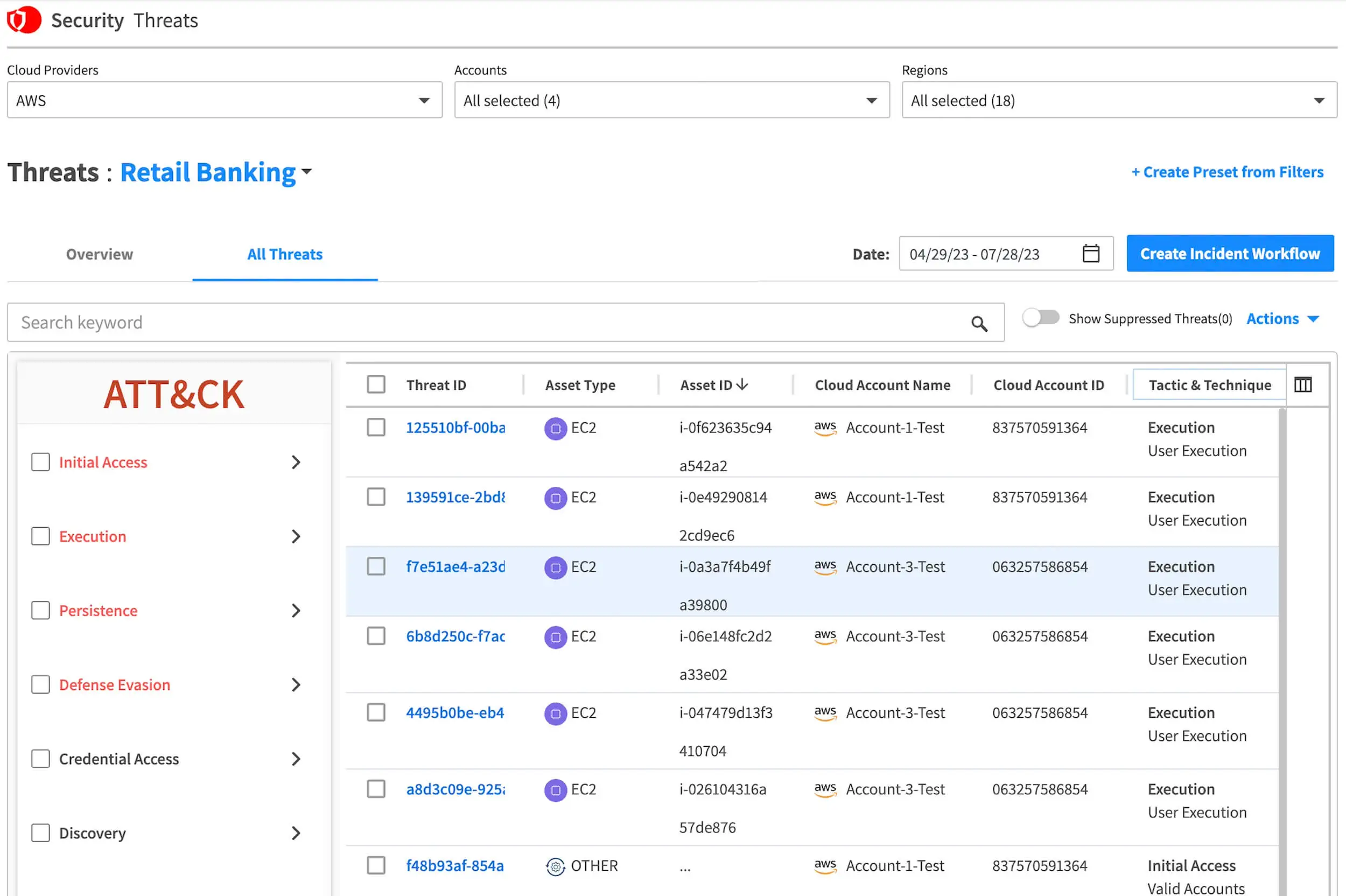
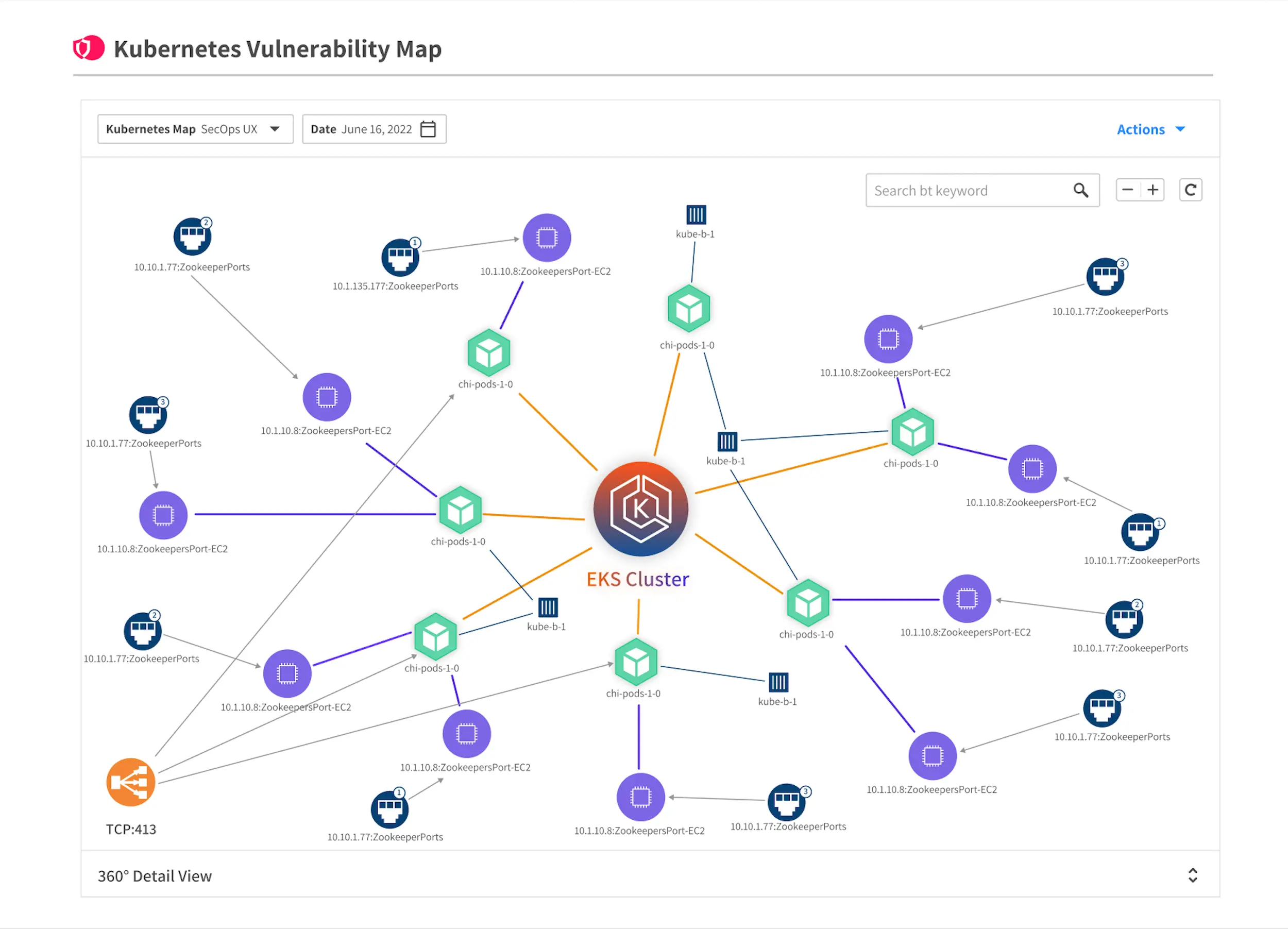
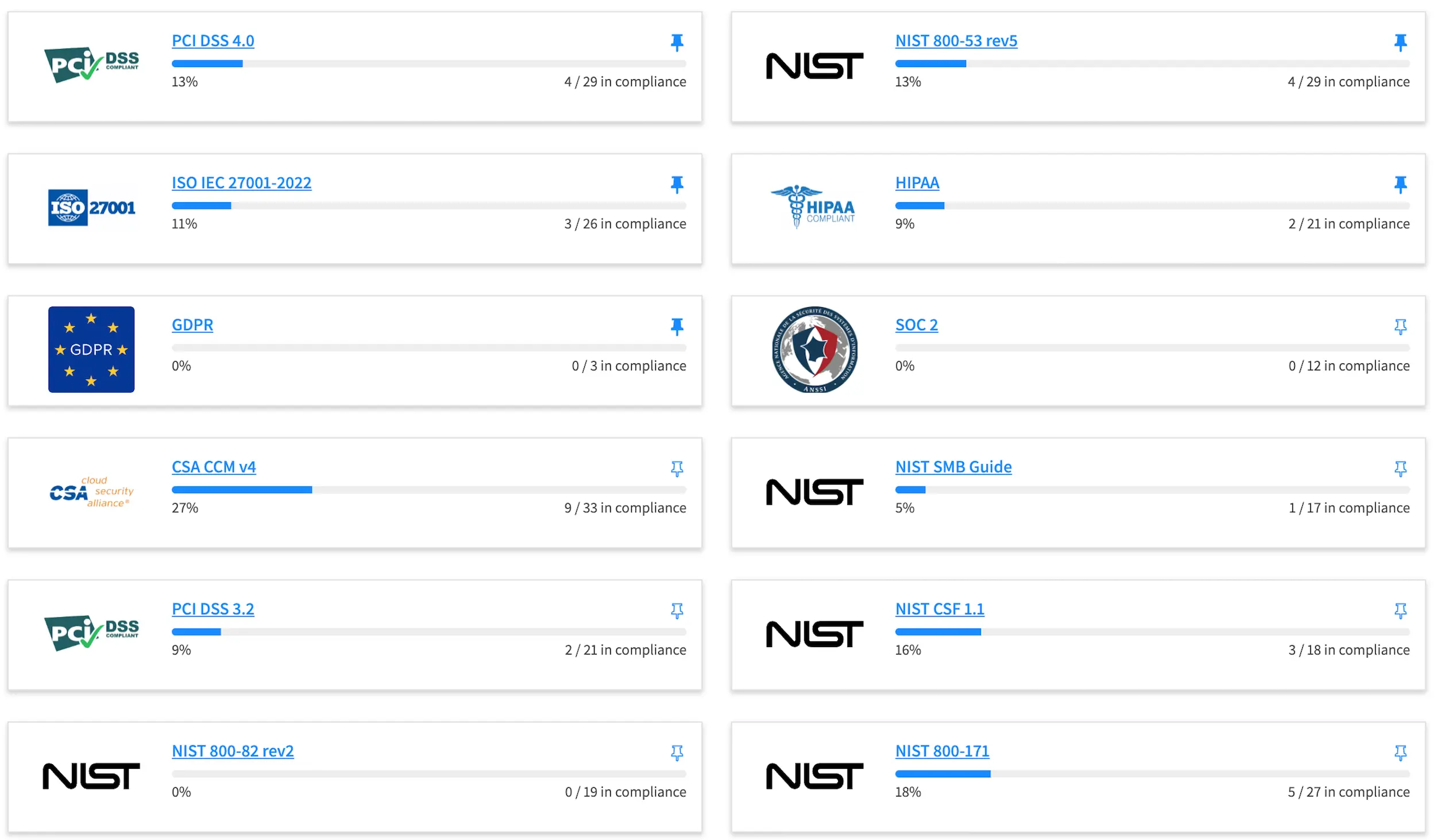
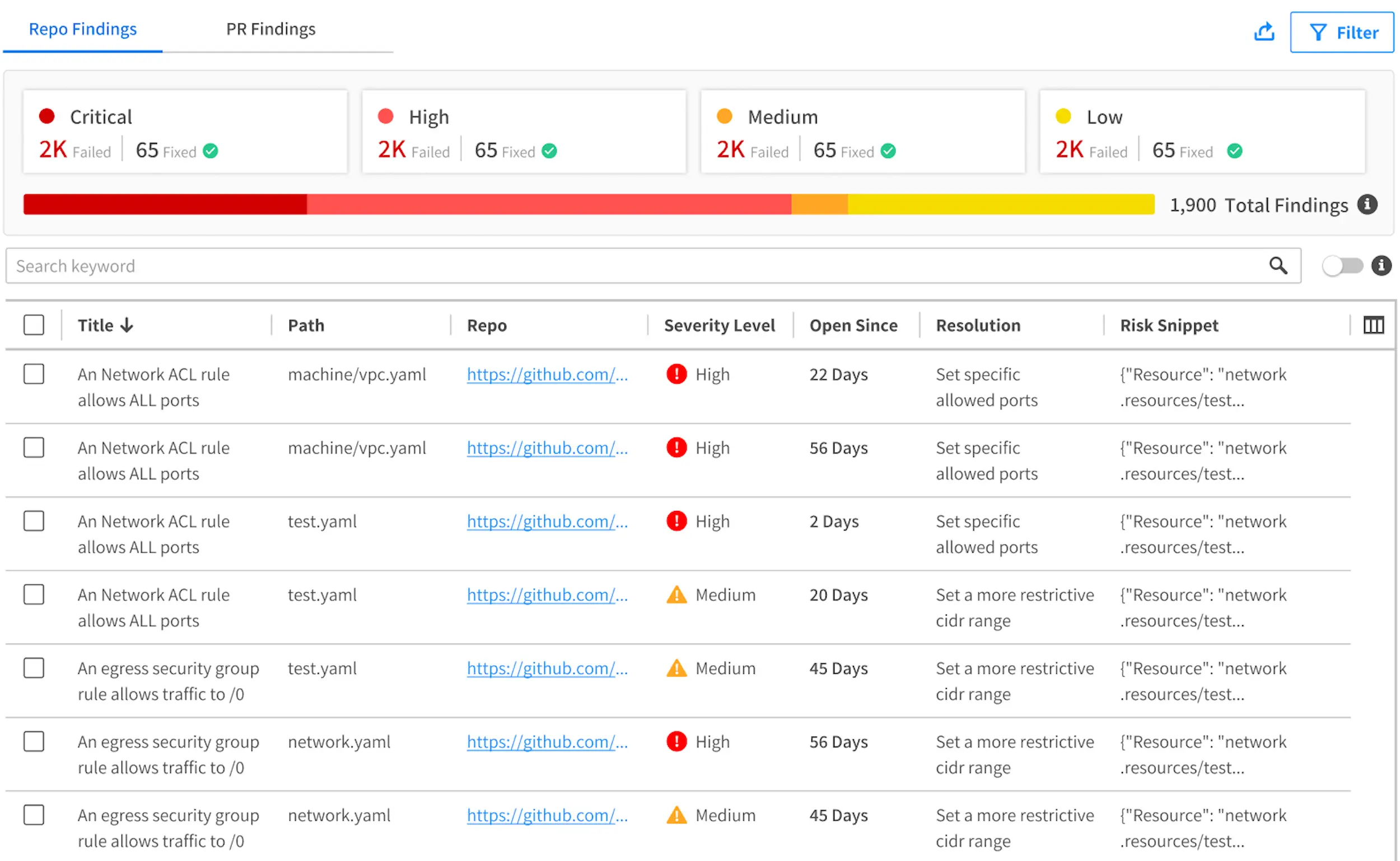
Get a prioritized 360-degree view of risk based on the severity, attack surface and network exposure – all in one dashboard.
Understand the risk impact
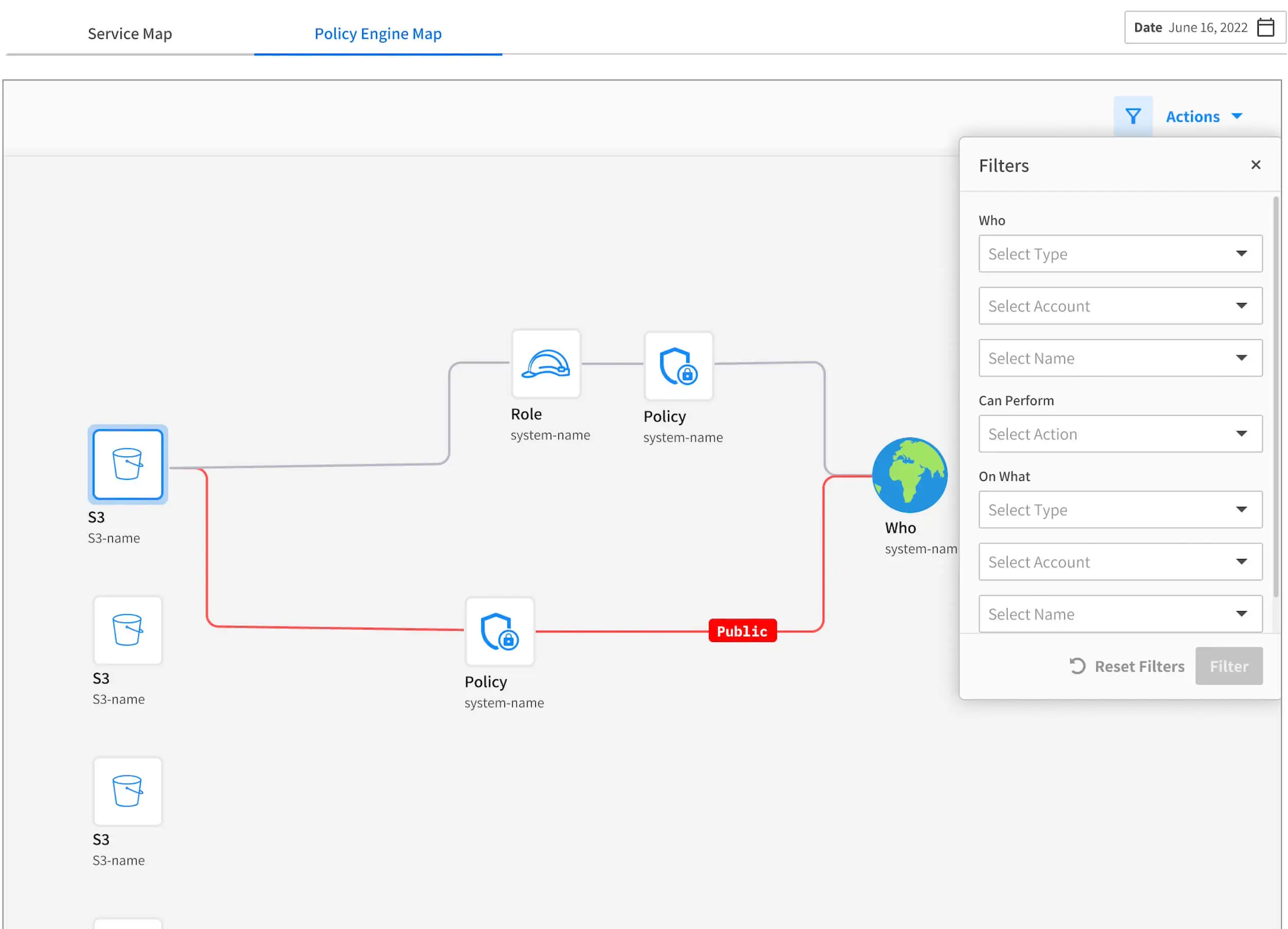
Correlate and contextualize risk attributes to prioritize the risks that have the greatest impact on your business.
Focus on the real risk to critical assets
Easily uncover even seemingly minor gaps in your security posture that put critical assets and IP at risk.
Remediate quickly and easily
Save time and effort with proactive alerting, guided or automated remediation and incident response workflows.